CREST has collaboration with government and industry.
Our Key Collaborators
Our Works
Keep Building
At CREST researchers are leveraging existing software engineering, analytical reasoning, natural language processing and machine learning tools and techniques to develop a secure and integrated platform. Our aim is to help build a secure and integrated platform that is easy to use and evolve with the changing threat landscape and increase the operation efficiency of the cybersecurity team.

Automatic Parameter Tuning for Big Data Analytics Frameworks
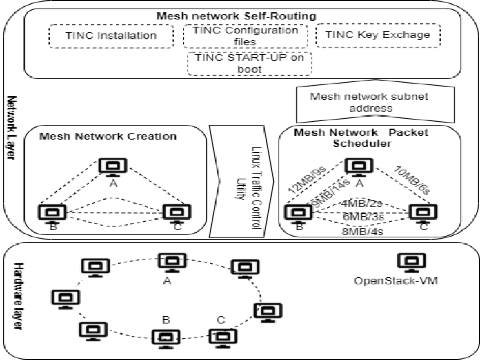
Design and Implementation of Fragmented Clouds for Evaluation of Distributed Databases & Big Data Analytical frameworks

Database Configuration, Workload parametrizations, and Cloud Configuration Tuning
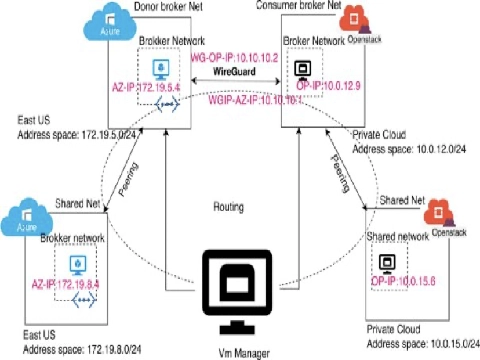
Performance evaluation of Big Data Analytical frameworks in hybrid clouds

Enhancing Security Data Quality with Human-Centric Visualization and Machine Learning

Supporting the Effective Use of Security APIs by Developers
Enhancing automatic program repair via large language model
Qualitative and Quantitative Software Vulnerability Analytics Using Open-Source Data
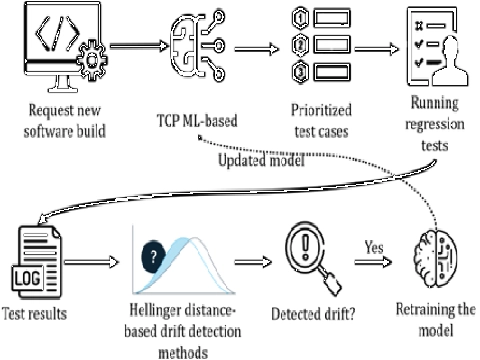
Maintaining ML4CI test case prioritization models through using data drift detection
Twitter Update From the Group
%
Loading 'crest_uofa' Timeline ...

Pursue your passion and work alongside world-recognized leaders in the field of software engineering. We invite you to view current employment opportunities, learn about benefits of working at the CREST, and apply for a position.